Social Engineering is an art of devious skill-sets put in action to exploit an error made by any individual — to access private and information. In the cyber-crime world, these “person hacking” scams are quite common and most of the people tend to disclose confidential data unknowingly, spreading virus infections, or giving access to prohibited systems.
A major of the scams based on social engineering are based around psychology i.e. how people think and act — useful to predict and manipulate the target’s behavior. Once an attacker finds out what a user will react to, or what attracts them, they can deceive and manipulate the user quite easily.
Besides, malicious attackers try to exploit the lack of knowledge of many users. Thanks to the speed of technology and growth of internet penetration in India, many consumers and employees aren’t aware of certain threats like drive-by downloads. Users in India also don’t realize the actual value of personal data, like their phone number further resulting in illiteracy on how to best protect themselves and their information.
Impersonating as an email from a friend:
If an attacker manages to hack or guess one person’s email password using social engineering, they will have access to that person’s contact list because most of user accounts have the contacts linked to it. Also because most people tend to use the same password everywhere, attackers can also gain access to that person’s other social networking accounts as well.
Once the attacker has the target’s email account under their control, they send emails to all the person’s contacts or leave messages on all social pages, and possibly on the pages of the person’s friends of friends, hence widening the vector of the attack by trying to reach to other accounts too.
Taking advantage of the target’s trust and curiosity, these messages might:
● Either contain an link that you just have to check out — and because the link comes from a friend and you’re curious, you’ll trust the link and click — and be infected with malware resulting in the attacker taking control over your machine and collect your valuable information and contacts and deceive others with them just like you were deceived.
● Or contain a series of pictures, music, movies, documents, etc., that has malicious scripts embedded in them. If you download — which you are likely to do since you think it is from your friend — you become infected. Now, the attacker has access to your machine, email account, social network accounts and contacts, and can thus spread the attack to everyone you know.
A majority of all social engineering attacks are dependent on the actual communication between the attacker and its targets. The attacker inclines to manipulate the user into compromising themselves, rather than using volatile and complex measures in order to gain access to the data.
Social engineering attacks follow generally follow a dependable process for deception of targets. Let us try and figure out this process for social engineering attack:
1. PREPARE by gathering background information on the target or a larger group that the target is part of
2. BUILD TRUST by establishing a relationship or initiating an interaction
3. EXPLOIT the target once trust is gained and target’s weaknesses are identified to advance the attack
4. DISSOCIATE with the target once the desired action has been executed by the target
This process can take a single day or over a period of time in a series of events. It could be face-to-face conversations, social media chats, mail exchanges, anything. But it concludes with an action which the attacker lures the target to take — sharing important information or exposing to threats only a well aware individual can avoid.
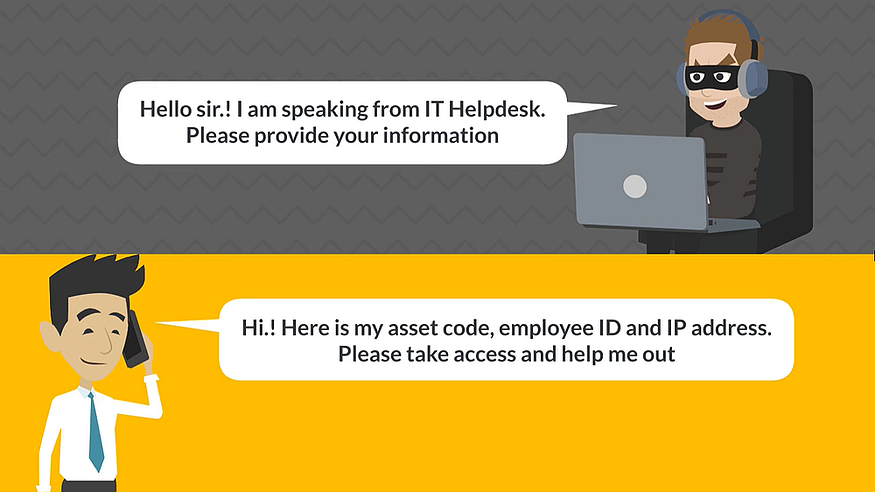
Many employees don’t realize that just a few pieces of information can give attackers access to multiple networks and accounts in their organizations. By impersonating as legitimate users to IT support personnel, the attackers try to gain your private details — like name, employee ID, IP address etc. Using this information, it becomes easier for the attackers to gain access to the employees system and then possibly escalating to the network as well. They can conduct crucial transactions, leak critical information, inject malwares in the system and network and more.
Almost every type of cyber-crime involves some kind of social engineering. Here are some conventional techniques used by social engineering attackers:
Phishing attacks which include spam phishing, spear phishing and whaling; voice based phishing (Vishing); SMS based phishing (SMiShing); Angler phishing which takes place on social media, Search engine phishing that attempts to place links to fake websites at the top of search results.
Baiting Attacks including USB drives left in public spaces, like libraries and parking lots or sending email attachments including details on a free offer, or fraudulent free software.
Physical breaches involving attackers posing as someone legitimate to gain access to unauthorized areas or information; Tailgating, or piggybacking — sneaking behind an authorized staff member into a restricted-access area.
So how would you protect yourselves from being a victim to social engineering attacks? Here are some recommendations:
● Delete all requests for financial information or passwords. If you get asked to reply to a message with personal information, it’s a scam.
● Reject all requests for help or offers of help. Legitimate companies and organizations do not contact you to provide help. If you did not specifically request assistance from the sender, consider any offer to ‘help’ restore credit scores, refinance a home, answer your question, etc., a scam. Similarly, if you receive a request for help from a charity or organization that you do not have a relationship with, delete it. To give, seek out reputable charitable organizations on your own to avoid falling for a scam.
● Set your spam filters to high. Every email program has spam filters. To find yours, look at your settings options, and set these to high-just remember to check your spam folder periodically to see if legitimate email has been accidentally trapped there. You can also search for a step-by-step guide to setting your spam filters by searching on the name of your email provider plus the phrase ‘spam filters’.
● Secure your computing devices. Install anti-virus software, firewalls, email filters and keep these up-to-date. Set your operating system to automatically update, and if your smartphone doesn’t automatically update, manually update it whenever you receive a notice to do so. Use an anti-phishing tools offered by your web browser or third party to alert you to risks.
Beyond deploying several security systems in your organization, this attack directly targets the first line of defense — your employees.! Don’t let this first line of defense be your weakest line of defense !! Well educated users will not only know how to protect their personal data, but also the organization’s all important data. With our Employee Awareness Program (P.E.A.P) which is combined with phishing simulation and training, your company can stay ahead of the ongoing security threats by securing the first line of defense.

